IoT is no longer a theory, but a force to be reckoned with in the business world. By embracing the interconnectivity of machines and devices, IoT has made machine-to-machine interactions smooth, not to mention championed the automation of most business tasks. One of the biggest winners are manufacturing companies, as IoT makes it easy to reduce costs in some of their production processes.
Although your business might not be a manufacturing firm, IoT can still be felt in its premises, from smart thermostats to wearable technology. Sadly, this comes at a cost as with easier flow of information comes easier channels for hackers to gain access to the most sensitive data of your business. While connected tools such as thermostats can offer information about the times when the office is occupied, manufacturing devices can lead to accessing your databases among other sensitive information.
Luckily, log management can be beneficial in beefing up IoT security if used wisely. Here is why you should consider integrating log management into your IoT environment:
Logging and IoT
Logging has existed for a long time in the business world. Through logging servers and logging platforms, IT leaders have managed to monitor their IT assets. This has made it easy to determine anomalies in the infrastructures as well as identify security threats and vulnerabilities before they can lead to any major losses.
IoT devices, on the other hand, need to function in optimal status to maintain machine to machine communication while protecting the data they transact at the same time. Monitoring the devices using log data offers IT professional enough threat intelligence to identify any loopholes that could lead to downtimes.
IoT Is Meant To Be Used Widely
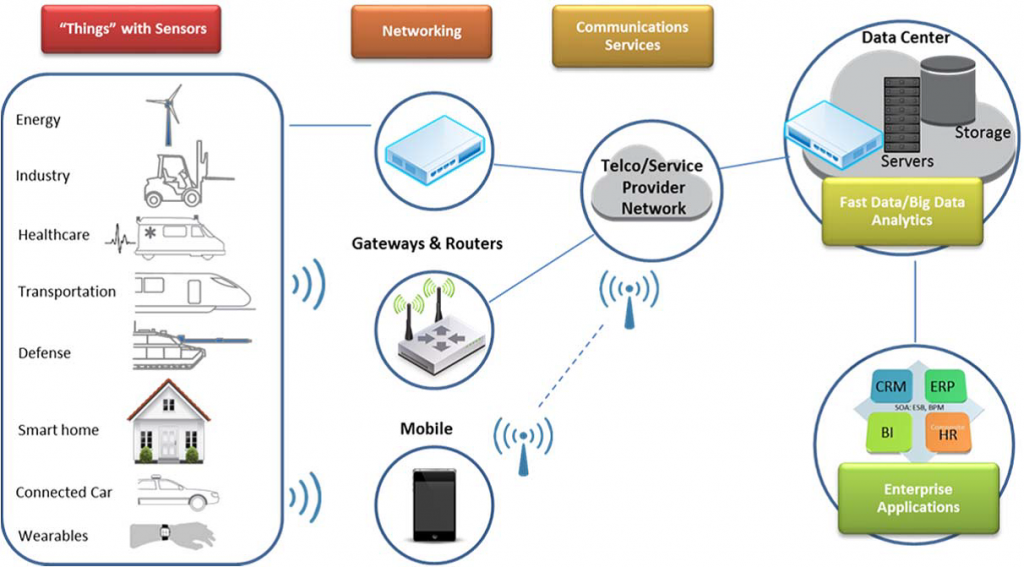
While the number of connected IoT devices is predicted to surpass 50 billion by the end of 2020, IoT is not preserved for the manufacturing environment alone. In fact, major cities are being built where ‘smartness’ is the order of the day. A good example is the Songdo city in South Korea.
Given that cars, doors and even cameras will all be connected to the internet, this will pose a threat to the whole city were hackers to gain access to the network. For IT professionals to prevent the potential damage that a cyber-attack could lead to, they need to be steps ahead of the attackers. Luckily, log management will provide them with enough intelligence to proactively protect future devices.
Network Level Defense Is No Longer Enough
The conventional way to safeguard company systems is through a network-level defense. IT professionals pay attention to what is coming into their infrastructure through their IT, they detect attacks and prevent intruders. Unfortunately, this method has its limitations which could easily lead to the failure of the company’s IoT investment efforts.
It is possible for hackers to façade their attacks in the form of regular traffic which might be tough to detect through the conventional means. Additionally, inspecting encrypted traffic is tough for most network-level security solutions. Instead, IT professionals should also include device level-security to closely monitor the log files on the device as well as the network for optimal security.
Manufacturers Might Not Embrace Security by Design
Some manufacturers look for cheap ways to produce devices into the market, but this is not the best foundation for the security of IoT devices. The devices need to be designed with security in mind by including aspects such as data encryption. Considering that IoT devices are poised to outlast other IT devices, it only makes sense to make updating them easy.