In years past, the network perimeter was considered the security control point for IT departments. As more and more data has moved to the cloud, making the concept of “perimeter” outdated and ineffective, enterprises are finding themselves wondering how they can properly secure their cloud applications in a similar way as they had done their in-house IT infrastructure.
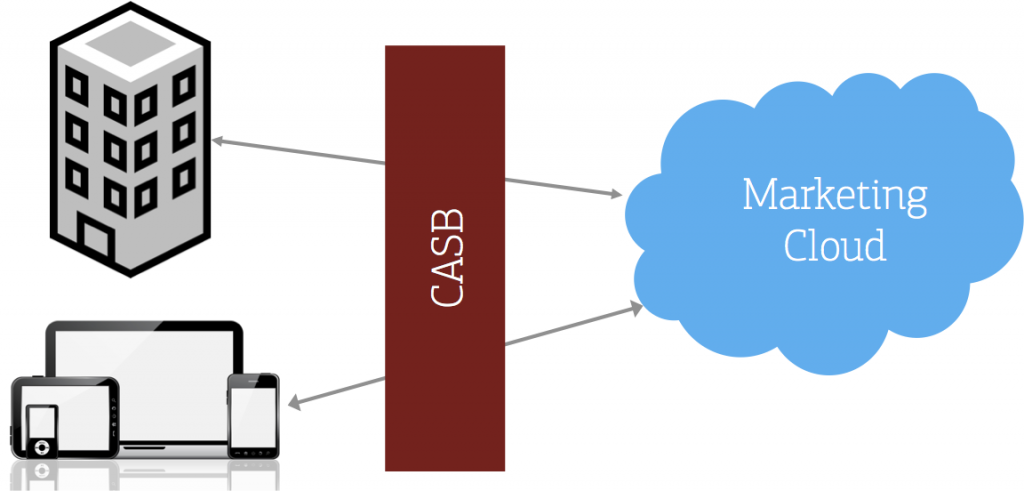
One emerging security category that is seeing rapid adoption amongst enterprises looking to secure their cloud services is cloud access security broker (CASB).CASBs are cloud software that protect corporate data that is bound for the cloud.They offer a wide range of capabilities, from more traditional data security such as encryption, to cutting edge features, like machine learning based threat protection.
As of 2015, the CASB market was worth $3.34 billion. However, experts believe that the value of the CASB market will more than double by 2020, reaching a value of $7.51 billion.
Why are CASBs becoming such a large part of information security? To understand that answer, you’ll need to first understand the role of the CASB.
What Is a CASB?
Image via Flickr by marklord photography
The emergence of the CASB category has been driven in large part due to the rapid pace with which enterprises are decommissioning their on-premises softwares and IT infrastructure in favor of the cloud.
The CASB technology monitors user activity, enforces security and compliance controls, and administer governance policies in the cloud. CASBs go one step further than what’s available in terms of security features native to a cloud service in that CASBs secure all SaaS applications in use at an enterprise.
With many companies switching over to CASBs for data protection, experts believe that about 85 percent of large enterprises will be a CASB them by 2020, up from 5% in 2015
What Does a CASB Do?
CASB capabilities can broadly be grouped within 4 categories: cloud visibility, cloud compliance, cloud data security, and cloud threat protection.
Visibility refers to a CASB’s ability to identity all the cloud application in use (both shadow and sanctioned), the amount and type of data being uploaded to the cloud services, and the security capabilities of each cloud application. With this capability, organizations can quantify not only their total cloud footprint, but also analyze the kind of security risk employees are putting sensitive corporate data in.
When it comes to cloud compliance, a CASB can help organizations extend certain security controls to the cloud so that the organization remains compliant with internal policies and external regulations. Given the steep fines that organizations incur when there is a data breach, as well as loss of reputation and customer trust, compliance becomes an important part of a CASB’s security offering.
The average employee is likely to use a very insecure password. To make matters worse, employees are known to use the same password across multiple services. This leaves enterprises open to data breaches caused by a compromised account. So much so that according to Verizon, 63% of data breaches result from weak or stolen passwords. Combine that with the success that hackers have with phishing users for their login credentials, and it becomes clear that compromised accounts pose a huge problem for most companies. A CASB’s cloud threat protection solution can detect compromised accounts, insider threats, and threats arising from malware.
Data security is another crucial capability of a CASB. Data security comes in several forms: applying peer-reviewed cloud encryption, enforcing access control policies, or applying eDRM (or IRM) to sensitive information.
The Importance of CASBs for Businesses
Now that you know a little more about how CASBs work, you can better understand the role they can play in your business. Installing and using a CASB can help your business in a variety of ways. First, CASBs find cloud services in use and accelerate the approval process of those cloud services with adequate security capability so that your employees can get work done faster and more efficiently.
In many ways, CASBs are business enablers, helping organizations take advantage of the benefits of the cloud while minimizing their inherent security risks.